What is Zero Trust Architecture?
Zero Trust Architecture (ZTA) is a security model that assumes no user, device, or network is inherently trustworthy. Instead, it requires continuous verification of every access request, regardless of location. Traditional perimeter-based security is obsolete in today's hybrid work environments, where threats like ransomware and insider attacks are rampant. As we approach 2026, predictions from cybersecurity experts forecast a surge in AI-driven hacks, supply chain breaches, and quantum computing exploits that will render legacy defenses useless.
The core mantra of zero trust is "never trust, always verify." This shift is essential because breaches have evolved: 95% of organizations experienced a cloud security incident in the last year, according to recent reports. Implementing zero trust enhances data privacy by enforcing least privilege access and micro-segmentation.
Core Principles of Zero Trust
Zero Trust is built on seven foundational principles outlined by leading frameworks:
- Verify Explicitly: Authenticate and authorize based on all data sources, not just identity.
- Least Privilege Access: Grant the minimum permissions necessary, dynamically adjusting as needed.
- Assume Breach: Design systems to limit blast radius and enable rapid detection.
- Micro-Segmentation: Divide networks into isolated segments to contain threats.
- Continuous Monitoring: Use AI and analytics for real-time threat detection.
- Automation and Orchestration: Streamline responses to reduce human error.
- Secure by Design: Embed security into every layer of the stack.
These principles directly counter 2026 threats, such as sophisticated phishing powered by generative AI and zero-day exploits targeting remote workforces.
Why Zero Trust is Essential for 2026 Hacking Threats
By 2026, Gartner predicts that 60% of enterprises will adopt zero trust, up from 10% today. Emerging threats include:
- AI-orchestrated attacks that mimic legitimate users.
- Quantum threats decrypting current encryption.
- IoT vulnerabilities in smart factories and cities.
- Supply chain attacks like SolarWinds, amplified by global tensions.
Zero trust mitigates these by eliminating implicit trust. For instance, even if credentials are stolen, contextual checks (device health, location, behavior) block access. Data privacy improves through encryption everywhere and just-in-time access, complying with GDPR and CCPA.
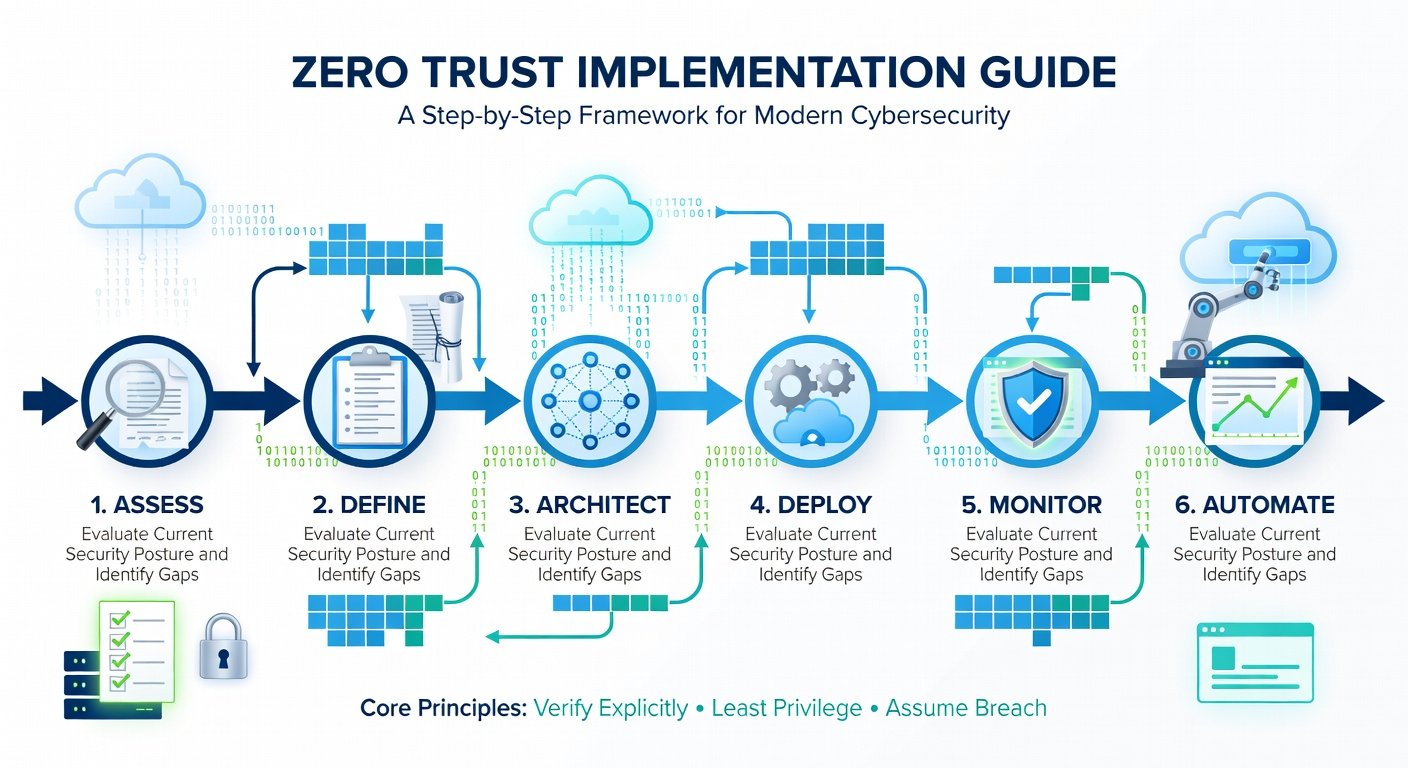
Step-by-Step Implementation Guide for Businesses
Transitioning to zero trust requires a phased approach. Here's a practical roadmap:
- Assess Current State: Map your attack surface using tools like Microsoft Zero Trust Guidance. Identify assets, users, and data flows.
- Define Protect Surfaces: Prioritize critical data and apps. Use risk-based scoring.
- Architect the Model: Choose a framework like NIST's. Implement identity (e.g., MFA everywhere), devices (endpoint detection), and networks (SDN).
- Deploy Policies: Roll out least privilege via role-based access control (RBAC) and just-in-time privileges.
- Enable Monitoring: Integrate SIEM with UEBA for anomaly detection.
- Automate and Test: Use SOAR platforms for incident response. Conduct red-team exercises.
- Scale and Optimize: Monitor metrics like mean time to detect (MTTD) and iterate.
Recommended Tools and Best Practices
Leverage these proven tools:
- Identity: Okta or Azure AD – For passwordless MFA and contextual access.
- Network: Zscaler or Palo Alto Prisma – Cloud-native SASE for micro-segmentation.
- Endpoints: CrowdStrike or SentinelOne – AI-driven EDR.
- Data: HashiCorp Vault – Secrets management.
Best practices for data privacy:
- Encrypt data at rest and in transit (use TLS 1.3).
- Implement data loss prevention (DLP) policies.
- Regular audits with tools like NIST Cybersecurity Framework.
- Train employees on phishing via simulated attacks.
Start small: Pilot with high-value apps before full rollout. Budget 10-15% of IT spend on security.
Case Studies of Successful Zero Trust Adoptions
Google BeyondCorp: Pioneered zero trust in 2009, eliminating VPNs. Result: No breaches from external perimeter attacks. Employees access resources via device posture checks.
Microsoft: Adopted enterprise-wide, reducing insider threats by 50%. They use Intune for device compliance and Defender for monitoring.
Financial Firm (e.g., Capital One Post-Breach): After a 2019 cloud breach, implemented zero trust with AWS and Okta, cutting unauthorized access attempts by 90%.
These cases show ROI: Average breach cost savings of $1.5M per incident, per IBM reports.
Common Pitfalls to Avoid
Don't rush—80% of failures stem from poor planning:
- Overlooking Legacy Systems: Use gateways to bridge old apps.
- Tool Silos: Integrate via APIs; avoid point solutions.
- Ignoring Culture: Train staff; change management is key.
- Skipping Metrics: Track KPIs like access denial rates.
- Compliance Over Security: Zero trust exceeds regs like HIPAA.
Partner with experts like CISA Zero Trust Resources for maturity models.
Conclusion: Secure Your Future Now
Zero trust isn't a product—it's a strategy. As 2026 threats loom, businesses ignoring it risk extinction. Start your journey today for resilient, privacy-focused operations. With disciplined implementation, you'll turn security into a competitive edge.



No comments yet. Be the first!