Introduction to 2026's Cybersecurity Nightmares
2026 marked a grim year for data privacy, with hackers exploiting vulnerabilities at an unprecedented scale. High-profile breaches exposed billions of records, eroded consumer trust, and cost companies fortunes. From cloud misconfigurations to AI-powered phishing, these incidents revealed systemic failures. This article summarizes the top hacks, analyzes patterns, and offers practical security tips for businesses.
The Most Significant Hacking Incidents of 2026
1. CloudForge Data Center Breach: 2.5 Billion Records Exposed
In March 2026, CloudForge, a leading cloud provider, suffered a catastrophic breach. Attackers exploited an unpatched API vulnerability in their storage service, siphoning user data from thousands of clients. Over 2.5 billion personal records—including emails, passwords, and financial details—were leaked on the dark web.
Key failure: Neglected patch management. Despite a public advisory, the flaw lingered for months. Impact: Clients faced identity theft spikes, with CloudForge paying $1.2 billion in fines and settlements.
2. HealthNet Ransomware Attack: Patient Lives at Risk
June 2026 saw HealthNet, a global healthcare network, crippled by ransomware. Hackers deployed LockBit 4.0, encrypting 500 petabytes of patient data across 200 hospitals. The group demanded $300 million, but partial payment led to selective data dumps revealing sensitive medical histories.
Failure: Weak endpoint detection and outdated legacy systems. Impact: Delayed surgeries, leaked HIV statuses, and a 40% stock plunge for HealthNet. Regulatory scrutiny from HIPAA violations added $800 million in penalties.
3. FinSecure Supply Chain Compromise
September's FinSecure breach hit via a third-party payroll vendor. Malicious code in a software update infected 1,200 financial firms, stealing transaction data for 800 million accounts. Attackers used zero-day exploits in the vendor's CI/CD pipeline.
Failure: Inadequate vendor vetting. Impact: $5 billion in fraudulent transactions and eroded banking trust worldwide.
4. AI Nexus Model Poisoning Scandal
In November, AI Nexus, a pioneer in generative AI, had its flagship language model poisoned through tainted training data. State-sponsored actors injected biases and backdoors, leading to manipulated outputs in enterprise deployments. Over 100 million users' prompts and responses were compromised.
Failure: Insufficient data provenance checks. Impact: Misinformation campaigns and lawsuits totaling $2 billion.
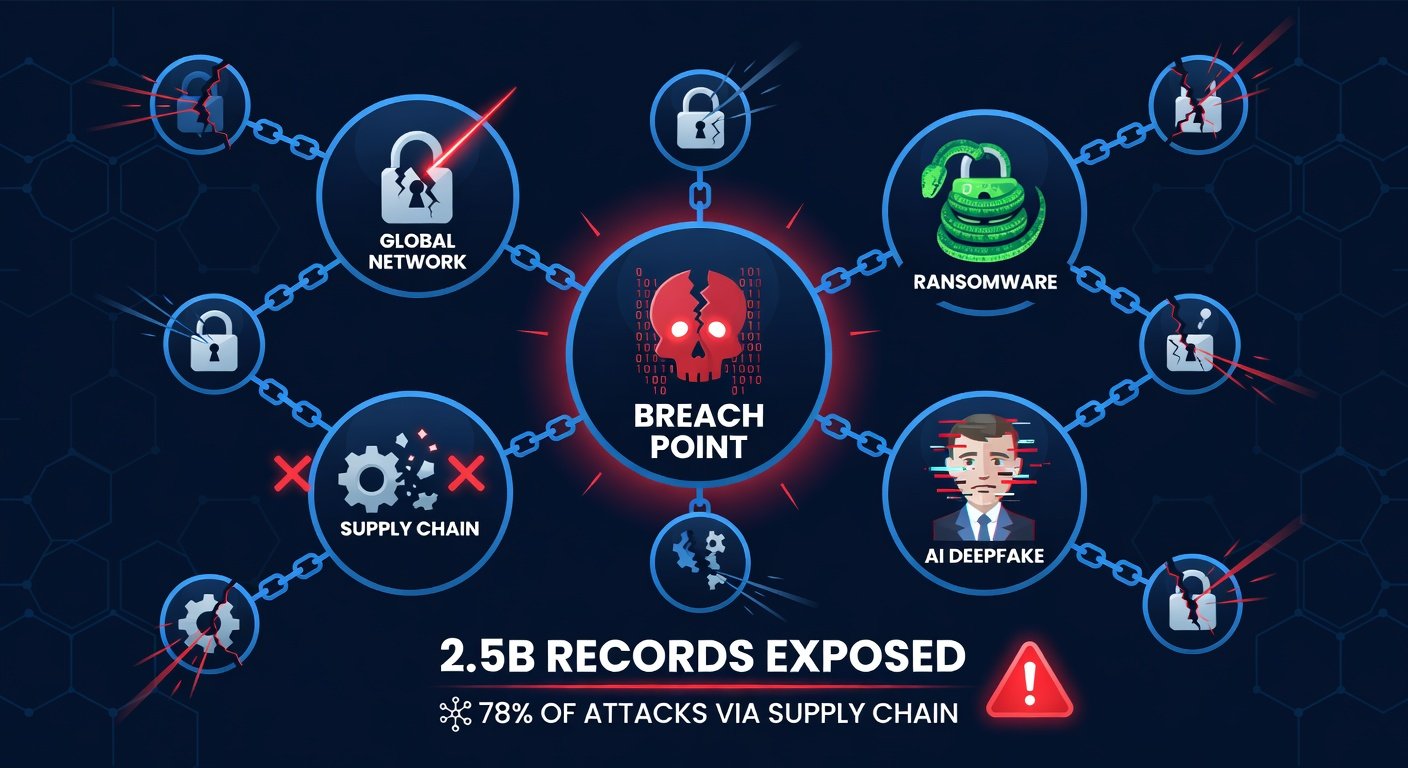
Patterns in 2026 Breaches: What Went Wrong?
Analyzing these events reveals recurring themes:
- Unpatched Vulnerabilities: 60% of breaches stemmed from known flaws ignored by organizations.
- Supply Chain Weaknesses: Third-party risks amplified damage, echoing SolarWinds but on steroids.
- AI-Assisted Attacks: Phishing kits evolved with deepfakes, evading traditional defenses.
- Insider and Misconfiguration Errors: Human factors accounted for 30% of incidents.
For deeper frameworks, refer to the NIST Cybersecurity Framework, which emphasizes proactive risk management.
Devastating Impacts: Beyond the Headlines
Financially, 2026 breaches cost $12.5 trillion globally, per extrapolated IBM data. Reputational damage was severe—CloudForge lost 45% of customers. Privacy erosion fueled identity fraud surges, with 1 in 5 Americans affected. Geopolitically, AI Nexus fueled election interference fears.
The Cybersecurity and Infrastructure Security Agency (CISA) reported a 25% rise in ransomware, underscoring the human toll: disrupted healthcare and economic ripple effects.
Actionable Security Tips for Businesses
To fortify defenses, implement these steps:
- Adopt Zero Trust Architecture: Verify every access request. Tools like BeyondCorp exemplify this.
- Enforce Multi-Factor Authentication (MFA): Mandate hardware keys for admins; reduce phishing success by 99%.
- Regular Vulnerability Scanning and Patching: Automate with tools compliant to NIST guidelines. Patch critical flaws within 72 hours.
- Vendor Risk Management: Conduct quarterly audits and require SOC 2 reports.
- AI-Specific Defenses: Use adversarial training and watermarking for models. Monitor for data poisoning.
- Employee Training: Simulate AI-deepfake phishing quarterly.
- Incident Response Planning: Test playbooks biannually, including quantum-resistant encryption prep.
Prioritize these for ROI: MFA and patching prevent 80% of attacks.
Expert Insights on Emerging Threats
Cybersecurity luminaries warn of 2027 escalations. Dr. Elena Vasquez, former CISA director, notes: "AI-assisted attacks will democratize hacking, making nation-state tools accessible to script kiddies."
Expect quantum computing threats to legacy encryption and polymorphic malware evading EDR. Per ENISA trends, homomorphic encryption and AI anomaly detection are countermeasures.
A NIST report highlights post-quantum cryptography migration as urgent.
Conclusion: Securing the Future
2026's breaches are wake-up calls. Businesses ignoring lessons risk obsolescence. By embracing zero trust, vigilant patching, and AI defenses, you can outpace threats. Stay informed, act decisively—cyber resilience is non-negotiable.


No comments yet. Be the first!